Secure authentication flows protect user accounts while preserving a smooth experience across devices and networks. Poorly designed flows frustrate users and create vulnerabilities that attackers exploit at scale. Modern apps must balance strong identity verification with low friction onboarding, recognizing that each added step reduces conversion. Security improves when teams design flows around realistic threat models rather than theoretical extremes. Clear communication helps users understand why protections exist, reducing abandonment during setup.
Threat Modeling and Risk Levels
Different actions carry different risk. Logging in from a new device or changing credentials warrants stronger verification than routine sessions. Adaptive authentication raises requirements when signals indicate elevated risk, such as unusual locations or rapid attempts. Risk based policies allocate friction where it matters most.
Credential Hygiene and Recovery
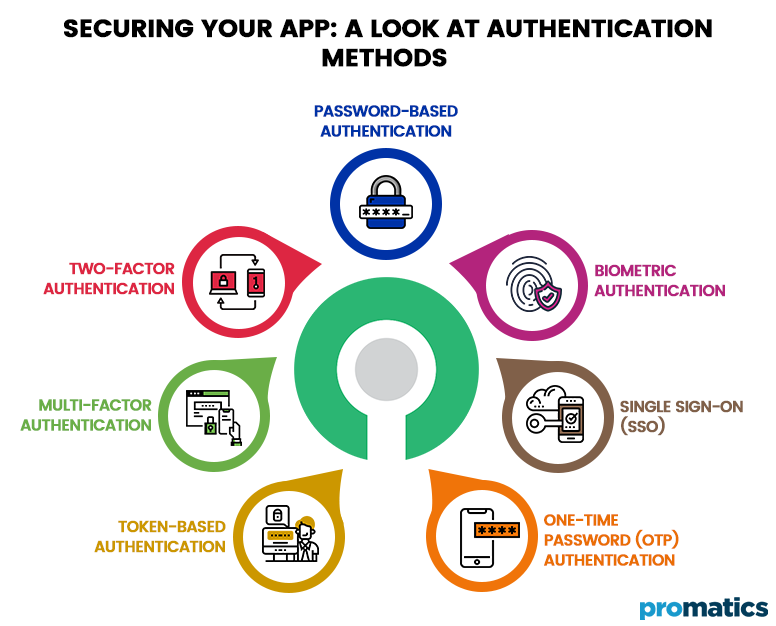
Passwordless options, hardware backed keys, and multi factor authentication reduce reliance on weak secrets. Recovery flows deserve as much design attention as primary login paths. Account recovery should verify identity without exposing data or enabling social engineering. Rate limits and monitoring deter abuse.
Telemetry and Continuous Improvement
Metrics on drop off, recovery success, and suspicious activity guide iteration. Regular reviews align security posture with evolving threats and user behavior.